Overview of quibids.com
Type: Browser hijacker \ Redirect Virus
Alert level: Severe
Risk Coefficient:Severe \ High Level
Targeted Browsers:Internet Explorer, Firefox, Google Chrome, and so on.
Targeted OS: Windows XP, Windows Vista, Windows 7, Windows 8.
Diffusion Paths:
1. Other computer threats on the system
P2P network
2. Spam email attachments
3. Freeware, applications, files and so on downloaded from the Internet.
4. Corrupt web sites, Internet pop ups, social networks, and etc.
Possible Plots of quibids.com
2) It can modify registry values for running automatically when you start Windows.
3) It can replace your homepage and web search engine to its own one.
4) It can redirect web searches to other unrelated sites.
5) It may add plug in to the web browser to arouse irritating pup ups.
6) It can be bundled with other computer threats.
7) It can slow down system performance include starting up, playing computer games, surfing the Internet, and so on.
8) It can monitor and record your online habits.
9) It allows the third access.
How to Remove quibids.com?
Detailed Manual Removal Instructions
Open Internet Explorer >> Click on Tools >> Click on Internet Options >> In the Internet Options window click on the Connections tab >> Then click on the LAN settings button>> Uncheck the check box labeled “Use a proxy server for your LAN” under the Proxy Server section and press OK.

2- Disable all the suspicious startup items related to quibids.com.
For Windows Xp: Click Start menu -> click Run -> type: msconfig in the Run box -> click Ok to open the System Configuration Utility -> Disable all possible startup items generated from quibids.com.
For Windows Vista or Windows7: click start menu->type msconfig in the search bar -> open System Configuration Utility -> Disable all possible startup items generated from quibids.com.
3- Remove add-ons:
Internet Explorer
1) Go to 'Tools' → 'Manage Add-ons';
2) Choose 'Search Providers' → choose 'Bing' search engine or 'Google' search engine and make it default;
3) Select 'Search Results' and click 'Remove' to remove it;
4) Go to 'Tools' → 'Internet Options', select 'General tab' and click 'Use default' button or enter your own website, e.g. Google.com. Click OK to save the changes.
Google Chrome
1) Click on 'Customize and control' Google Chrome icon, select 'Settings';
2) Choose 'Basic Options'.
3) Change Google Chrome's homepage to google.com or any other and click the 'Manage search engines...' button;
4) Select 'Google' from the list and make it your default search engine;
5) Select 'Search Results' from the list remove it by clicking the "X" mark.
Mozilla Firefox
1) Click on the magnifier's icon and select 'Manage Search Engines....';
2) Choose 'Search Results' from the list and click 'Remove' and OK to save changes;
3) Go to 'Tools' → 'Options'. Reset the startup homepage or change it to google.com under the 'General tab';
4- Press CTRL+ALT+DEL to open Windows Task Manager and end all running processes.

5- Open the Registry Editor and delete all registry entries:
(Steps: Hit Win+R keys and then type regedit in Run box and click on OK)


HKCUSoftwareMicrosoftWindowsCurrentVersionInternet Settingsrandom HKCUSoftwareMicrosoftWindowsCurrentVersionPoliciesExplorerDisallowRun HKCUSoftwareMicrosoftWindowsCurrentVersionRunrandom HKEY_LOCAL_MACHINESOFTWAREMicrosoftWindows NTCurrentVersionWinlogon "Shell" = "[random].exe"
Detailed Automatic Removal Instructions
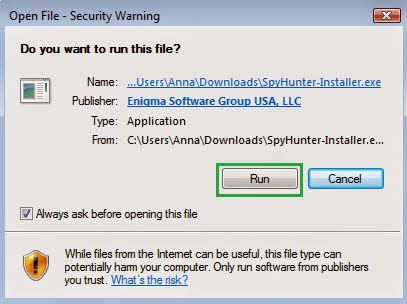
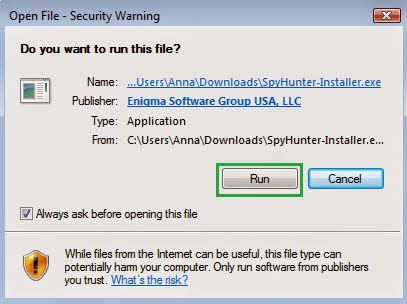
1) Click the icon below to download Spyhunter.

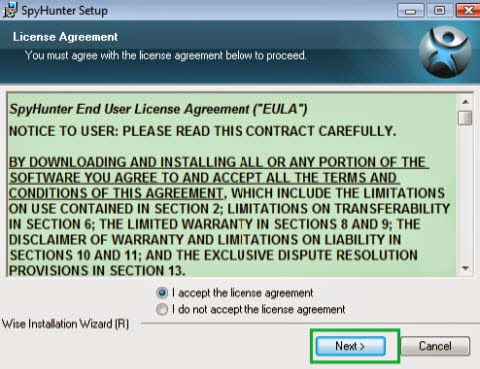
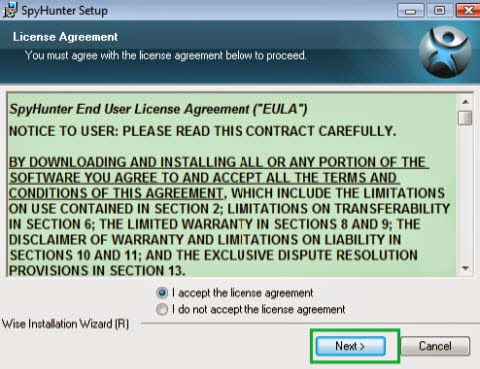
2) Install Spyhunter Step by Step:

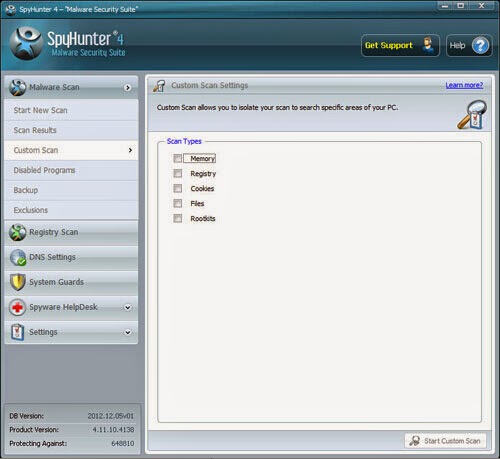
3) Start a full and quick scan with SpyHunter .
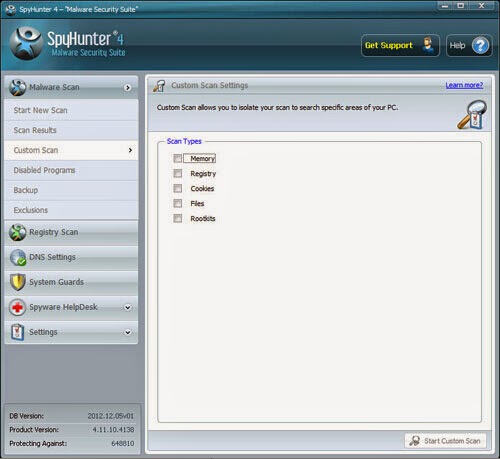.jpg)
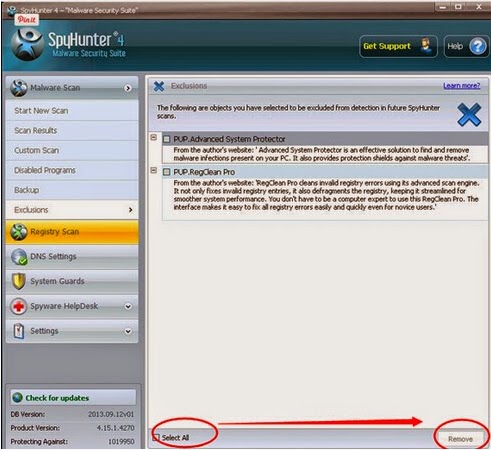
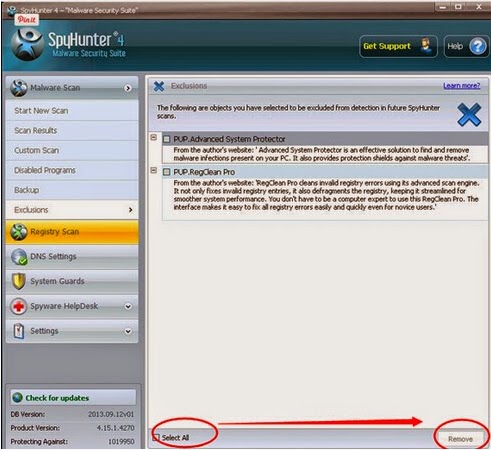
4) Remove detected threats.
Note 
2) Install Spyhunter Step by Step:

3) Start a full and quick scan with SpyHunter .
.jpg)
4) Remove detected threats.
The above manual removal is quite dangerous and complicated. And it also needs sufficient professional skills. Therefore, manual removal is a risky job. If any mistakes are made in the process, you may damage your computer immediately. So I recommend you to download and install Anti-Malware program SpyHunter. It is easy, efficient and automatic. What’s more, it won’t damage your computer. It serves not only a role of removing the malware program, but also a role of protecting your computer from threats in the future.

No comments:
Post a Comment