Trojan horse backdoor.Generic_c.FHP is created by cyber criminals for the purpose of making profits. It can track your online activities and use them to steal your money. Sometime, this data is sent to the third parties to get profits. A few days later, you will receive a lot of pop-up ads according to your browsing interests. Moreover, this virus can give access to other malicious computer threats which will be really dangerous to your computer system. At that time, your whole computer performance will be highly degraded and you are not able to get access to the Internet or program you like. In a word, what you need to do now is to get rid of Trojan horse backdoor.Generic_c.FHP from your PC soon.
1) Boot your computer into Safe Mode with Networking.
To perform this procedure, please restart your computer and keep pressing F8 key until Windows Advanced Options menu shows up, then using arrow key to select “Safe Mode with Networking” from the list and press ENTER to get into that mode.

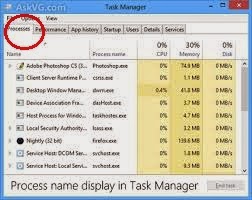
2) Press Ctrl+Alt+Del keys together to pull up Window Task Manager and end suspicious processes:
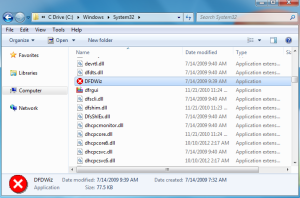
3) Check the following directories and remove all these associated files:
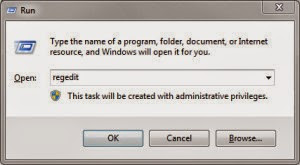
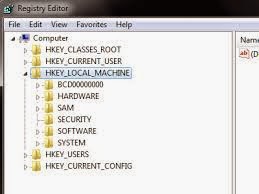
4) Open Registry Editor by navigating to Start Menu, type in Regedit, and then click OK. When you have been in Registry Editor, please remove the following related registry entries:
5) After you finish the above steps, please reboot your computer and get in normal mode to check the effectiveness.
The Effective Guide to Remove Trojan horse backdoor.Generic_c.FHP popups - Manual Removal Support
SpyHunter is a world-famous real-time malware protection and removal tool, which is designed to detect , remove and protect your PC from the latest malware attacks, such as Trojans, worms, rootkits, rogue viruses, browser hijacker, ransomware, adware, key-loggers, and so forth. To keep SpyHunter Anti-malware on your computer is an important way to protect your computer in a good condition. Please find the instruction as follow.
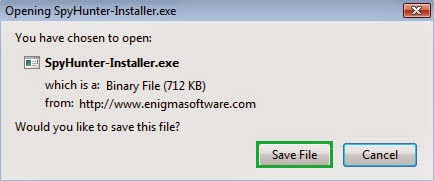
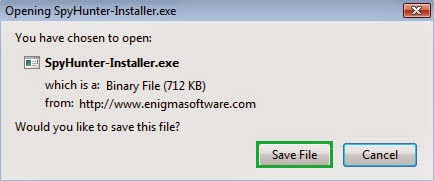
Step 1: Press the following button to download SpyHunter.
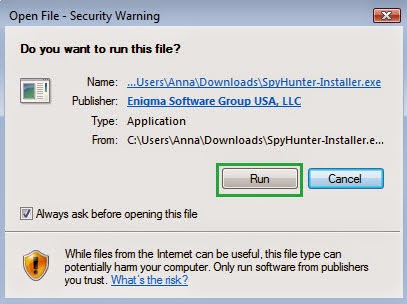
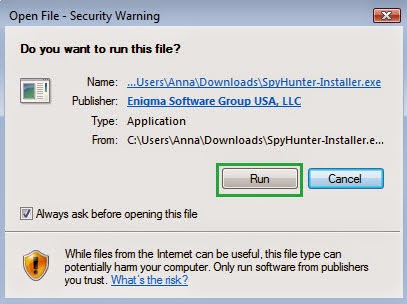
Step 2: Save the file onto your computer and click on the Run button to install it.
Step 3: After finishing the installation processes, scan your computer to find out potential threats.
6158)AZRTJ6S.jpg)
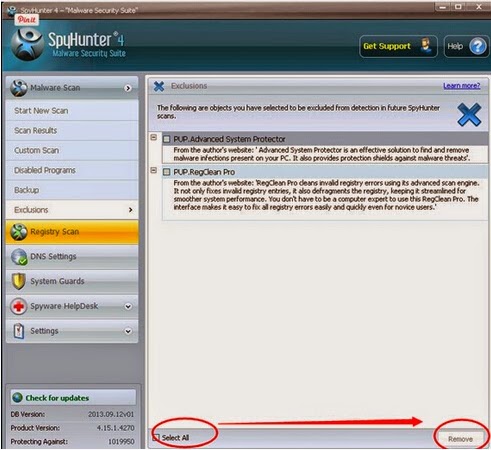
Step 4: Tick Select all and then Remove to delete all threats.
Guide to download RegCure Pro to optimize PC
If you are still worried about the left over of Trojan horse backdoor.Generic_c.FHP and want to clean all the unwanted registry entries, it is recommended to use RegCure Pro.
Step 1. Install and launch RegCure Pro on your PC.
Step 2. Select "Yes" to download and install RegCure Pro.

Step 3. Click "Next" to continue.

Step 4. RegCure Pro will open automatically on your screen.

Step 5. RegCure Pro is scanning your PC for error.

Step 6. After scanning, choose the issues you want to fix.





Step 6. After scanning, choose the issues you want to fix.


No comments:
Post a Comment