Trojan.Newarxy Description
After Trojan.Newarxy getting in successfully, it will immediately modify the original files, folders, settings, etc. Trojan.Newarxy usually is controlled by a remote hacker who serves as the third party. Once a connection is established, the hacker can manipulate the infected computer and perform many actions. Trojan.Newarxy can execute the harmful files. Both files and registry data may change due to the hacker’s interference. By giving a command for Trojan’s running, Trojan.Newarxy will create a backdoor for more viruses’ getting in. It can steal your confidential data which are stored on your computer. Sometimes, Trojan.Newarxy can affect the network connection. It can interrupt the network or slowdown the computer’s running system.
The Removal of the Trojan.Newarxy
Means 1: Using the manual ways to get rid of the Trojan.Newarxy
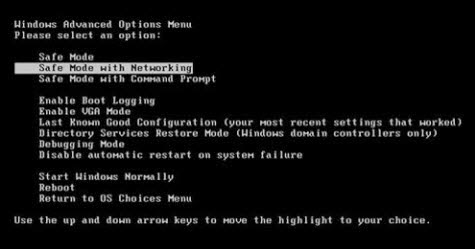
1) Reboot your computer. Before the Windows begins to load, press the “F8”key constantly.
2) Select the "Safe Mode with Networking" option, and then press Enter.
Step 2:
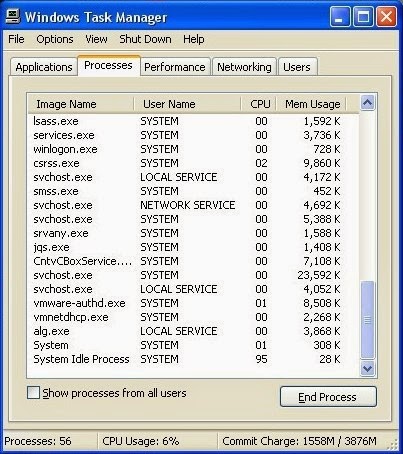
1) Launch the Task Manager by pressing keys Ctrl+Alt+Del or Ctrl+Shift+Esc at the same time.
2) Search for Trojan.Newarxy processes. Choose and end them.
Step 3:
1) Open Control Panel and search for Folder Options.
2) When you are in the Folder Options, click its View tab. Choose“Show hidden files, folders and drives” and tick “Hide protected operating system files (Recommended)”.
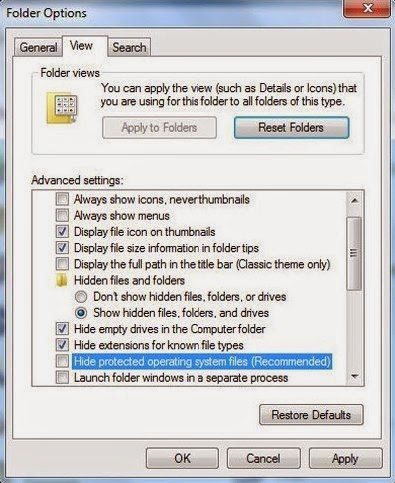
3) Select and remove the Trojan.Newarxy and related programs.
Means 2: Using the automatic ways to get rid of the Trojan.Newarxy
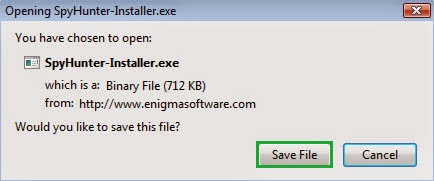
2) Execute the installation by double-clicking the download file.
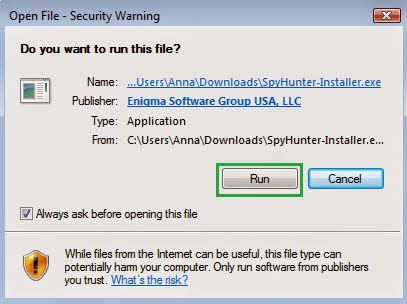
3) Now you need to click the “Run” button to permit the process’s installation.
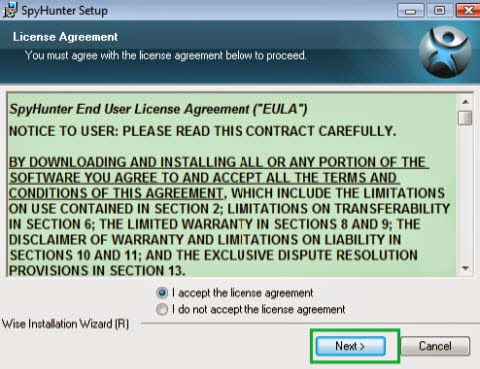
4) Next you should accept the License Agreement and click the “Next” button.
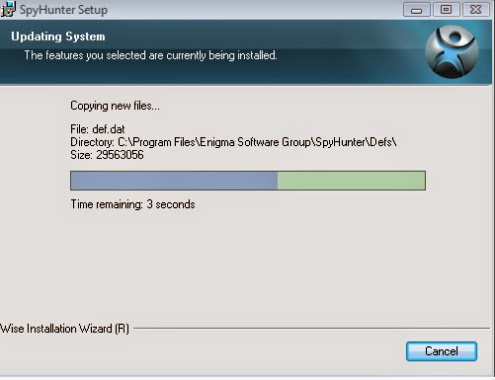
5) You need to wait until the whole installation finishes. In this process, you can not click the “Cancel”button; otherwise the process will be interrupted.
6) Now the installation finishes.

7) After finishing the installation, now you should click “Malware Scan” button to have a quick or full scan on your computer

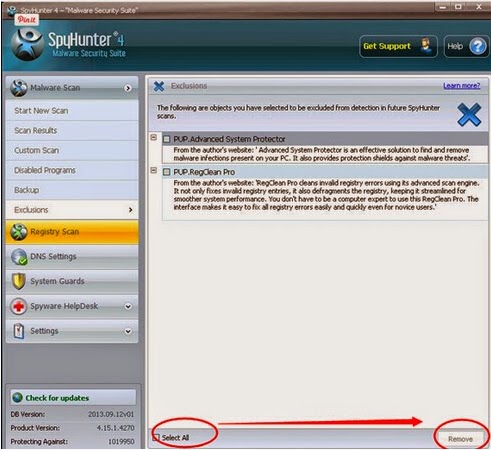
8) Tick the “Select All” and choose the “Remove” button to eliminate the detected threats on your computer.

No comments:
Post a Comment